Adopt the Cloud with Confidence
LEAD A SUCCESSFUL TRANSFORMATION
Cloud adoption across the enterprise is a significant undertaking that requires significant experience to successfully accomplish.
Our team of experts will prepare the organization for the transition to the cloud. We develop Enterprise views into your organization to allow leadership to make informed, fact-based decisions. By empowering decision-makers to understand the best method and timing for transitioning of solutions and services, we ensure the readiness of your organization in advance of cloud offerings.
We work with many industry vendors and cloud providers. We are not bound to specific solutions and will provide objective and reliable advice that fits your current and future business needs.
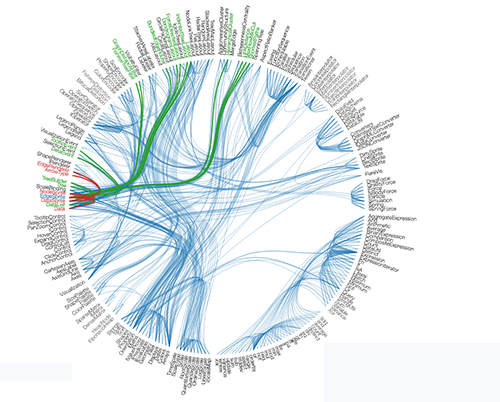
Six Organizational Views
MAKE INFORMED DECISIONS
Comprehensive assessment of your organization.
Accelerate your Cloud Initiative.
PLAN YOUR CLOUD OFFERINGS WITH US
Readiness View
ENSURING A SUCCESSFUL TRANSITION
Comprehensive assessment of the current and target states to enable high-level prioritization of cloud adoption initiatives including transition costs and organizational impact.
Application Portfolio Analysis: Portfolio of applications that are used by the organization to assess each against predefined factors.
Target Platform Capabilities: Organizations having existing IT capabilities will need to determine how their platform will evolve for cloud adoption, and whether existing technology systems and services can be leveraged.
Solution View
ENABLING CLOUD OFFERINGS
The cloud delivers unparalleled agility, efficiency and innovation, but only when implemented through a comprehensive cloud strategy. Architectural decisions in a traditional non-cloud environment are "point-in-time". These hinder the system’s ability to deliver solutions for changing business requirements. In the cloud, the capability to automate and test on demand lowers the risk of impact from design changes. This allows systems to evolve over time so that businesses can take advantage of new innovations as a standard practice.
Architecting for the cloud requires a comprehensive understanding of the factors contributing to an effective design. These include but are not limited to:
- Reliability: Ability to recover from infrastructure or service failures and mitigate disruptions.
- Performance Efficiency: Optimizing computing resources to meet dynamic and long-term demand.
- Cost Optimization: Expenditure awareness and the ability to eliminate suboptimal resources through continual re-assessment over time.
- Security and Compliance: Implementing best practices and design patterns while ensuring adherence standards.
Security View
ENSURING SAFE CLOUD SOLUTIONS
Provides a comprehensive, multi-level view into the organization to articulate the security principles, quantify risks and identify the posture necessary for the company to evolve and operate safely.
Overlooking critical risks posed by misunderstood security and governance can have detrimental effects on your business. When considering the cloud, organizations should ensure healthy operational processes, standards, compliance and disaster recovery are built into every cloud computing implementation. A sound security architecture must be embedded within the infrastructure to ensure security and privacy by design.
Governance, risk, and compliance (GRC) planning is essential for maximizing the value of your cloud implementation and includes policy-driven governance solutions around resources in private and public clouds as well as controlling access to critical cloud-based services.
- Governance provides for the ability to manage authority and accountability across the cloud environment through a shared responsibility model.
- Risk management provides for the ability to make good decisions based on an understanding of the risks throughout the design, build, and run lifecycle.
- Compliance provides for alignment with internal policy as well as third-party assurance frameworks in the design and deployment of workloads.
- Foundational: Identity and access management, logging/monitoring, infrastructure security, data protection, and incident response.
- Essential: Compliance validation, secure continuous integration and continuous delivery (CI/CD), configuration and vulnerability analysis, and security for big data and predictive analytics.

Considering the cloud?
Contact us to discuss options for cloud adoption.

